142 results found
CyberSolace Limited
External Cyber Threat & Digital Brand Protection Solution
CyberSolace’s unified Digital Brand Protection and External Attack Surface Discovery solution is a...
Squalify RQx GmbH
Squalify - Top-Down Cyber Risk Quantification
Squalify brings Cyber Risk Quantification (CRQ) to the boardroom. Backed by Munich Re’s real-world...
Codacy
Codacy Toolbox
Codacy's Toolbox ensures clean code. Our platform brings together a market-leading blend of tools...
Atos Group
AI-Driven Managed Detection and Response
Atos's MDR service is a next-gen cybersecurity solution that leverages AI and cybersecurity mesh to...
Whalebone
DNS4GOV
DNS4GOV is a government-oriented initiative to implement large-scale centralised protection for GOV...
WithSecure
WithSecure Elements XDR
WithSecure Elements Extended Detection and Response (XDR) is a unified solution, designed to protect...
Cyberday
Cyberday
Framework-Based Cybersecurity Cyberday offers a framework-based approach to cyber security...
Secure Practice
PrepJam by Secure Practice
Secure Practice is the European leader in cybersecurity awareness and preparedness. Kickstart your...
CyberDesk
Identity-Centric Data Security
CyberDesk helps you to adaptively control who can perform what actions with what data. Covering both...
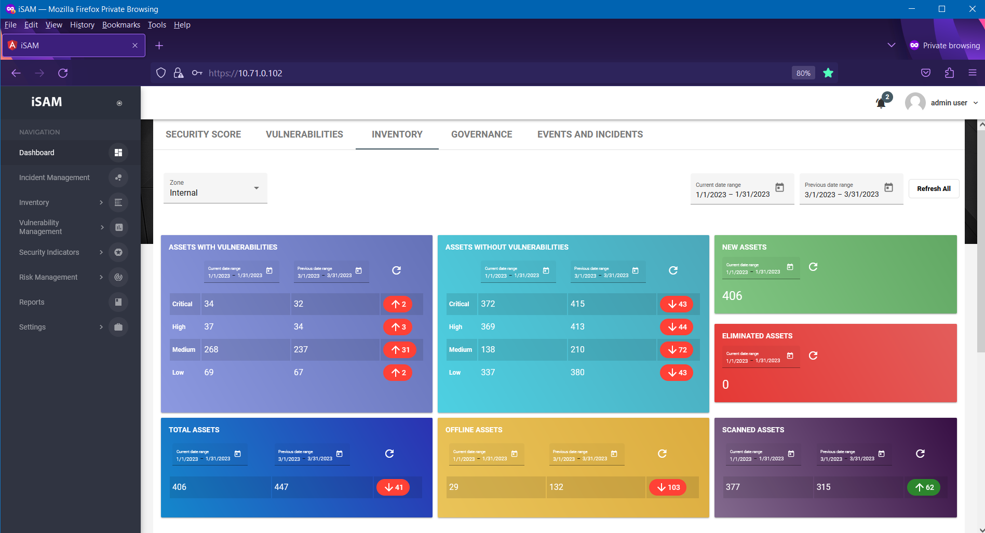
Safetech Innovations
iSAM - Information Security Automation Manager
iSAM is a product developed by Safetech Innovations, in order to ensure automation in the...
Binalyze
Binalyze AIR
Binalyze AIR is an investigation and response automation platform powered by forensic-level...
Threema GmbH
Threema Work. The Secure Business Messenger
Threema Work is a secure and GDPR-compliant business communication solution that facilitates mobile...